With RAID modern technology, information can be mirrored on one or more other disks in the exact same selection, to ensure that if one disk falls short, the data is kept. Many thanks to a procedure known as “striping,” RAID also provides the alternative of reading or composing to more than one disk at the exact same time in order to improve efficiency. In this setup, consecutive data is gotten into sectors which are sent to the numerous disks in the array, speeding up throughput. Likewise, due to the fact that a RAID selection utilizes a number of disks that appear to be a single gadget, it could frequently offer more storage capability than a solitary disk.
RAID tools utilize lots of various architectures, depending on the preferred balance in between performance and fault tolerance. These architectures are called “degrees.” Specification RAID degrees feature the following: Degree 0 (candy striped disk range without fault tolerance), Degree 1 (mirroring and duplexing), Degree 2 (error-correcting coding), Level 3 (bit-interleaved ), Degree 4 (committed parity drive), Degree 5 (block interleaved distributed parity), Degree 6 (independent information disks with dual ) and Degree 10 (a stripe of mirrors). Some tools utilize more than one degree in a hybrid or nested plan, and some vendors additionally offer non-standard proprietary RAID degrees.
RAID History and Alternatives
Prior to RAID devices became popular, the majority of systems utilized a solitary drive to store data. This setup is sometimes referred to as a solitary huge expensive disk or SLED. Nevertheless, SLEDs have some downsides. First, they can produce I/O traffic jams given that the data can not be read from the disk rapidly sufficient to keep up with the other elements in a device, particularly the processor. Secondly, if a SLED falls short, all the information is shed unless it has been just recently backed up onto an additional disk or tape.
In 1987, three University of The golden state, Berkeley, researchers– David Patterson, Garth A. Gibson, and Randy Katz– first defined the term RAID in a paper labelled An Instance for Redundant Arrays of Inexpensive Disks (RAID). They theorized that spreading data around a number of drives could possibly improve device performance, lesser costs and decrease power intake while preventing the possible integrity issues intrinsic in using cost-effective, and much less trustworthy, disks. The paper also described the 5 original RAID levels.
Today, RAID modern technology is virtually ubiquitous among company storage space devices and is additionally discovered in numerous high-capacity customer storage space devices. Nonetheless, some non-RAID storage space options do already existing. One option is JBOD, brief for “Simply a Number of Drives.” JBOD architecture uses a number of disks, yet each disk in the device is attended to independently. JBOD provides enhanced storage capability versus a solitary disk, yet doesn’t supply the exact same mistake resistance and efficiency benefits as RAID devices.
One more RAID alternative is concatenation or reaching. This is the technique of combining numerous disk drives to make sure that they appear to be a solitary drive. Covering increases the storage space capability of a drive; nonetheless, just like JBOD, reaching does not provide dependability or speed benefits.
RAID must not be confused with information backup. Although some RAID levels do offer redundancy, professionals suggest using a separate storage system for backup and disaster recovery functions.
Applying RAID
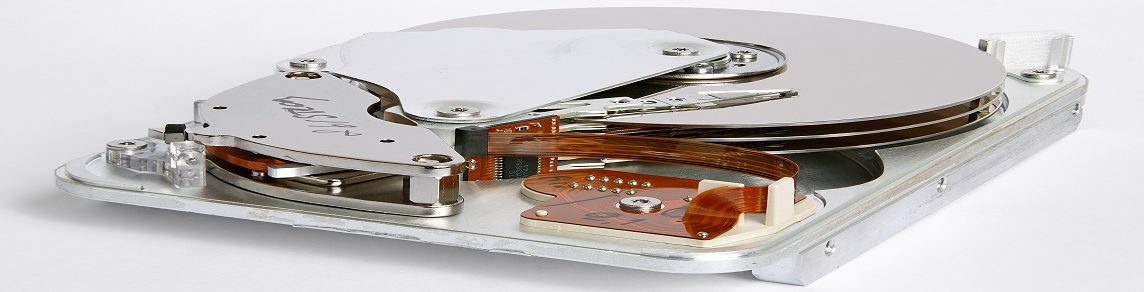
In order to set up a RAID variety, you’ll need a group of drive and either a software or an equipment operator. Software program RAID runs directly on a server, utilizing web server sources. Consequently, it might create some applications to run more gradually. Most server running devices feature some built-in RAID administration abilities.
You can additionally establish your very own RAID array by including a RAID operator to a server or a desktop computer PC. The RAID operator runs essentially the same software, however it uses its very own processor as opposed to the system’s CPU. Some cheaper “phony RAID” controllers offer RAID administration software program however don’t have a different processor.
Additionally, you can purchase a pre-built RAID variety from a storage space vendor. These home appliances usually consist of two RAID controllers and a group of disks in their own real estate.
Using a RAID variety is usually no various compared to making use of any other kind of main storage. The RAID management will certainly be managed by the hardware or software controller and is generally undetectable to the end user.